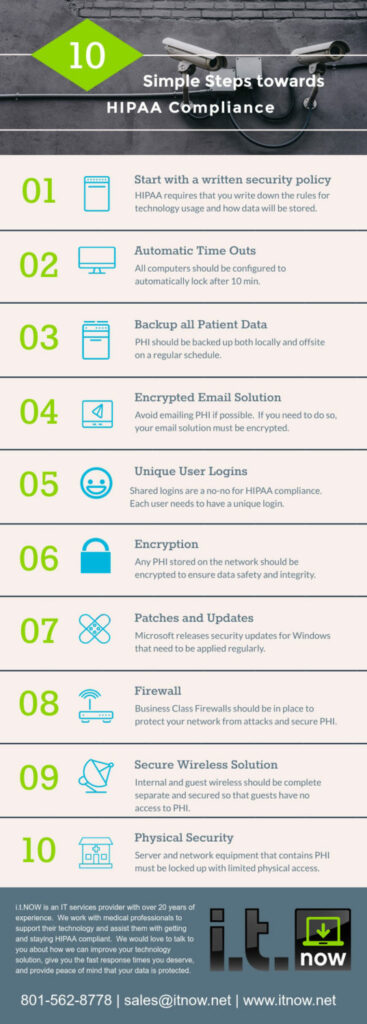
10 Simple Steps Towards HIPAA Compliance
Every project has to start somewhere right? For most healthcare administrators the task of HIPAA compliance is daunting and time consuming. The kind of project that is so intimidating that you put it off and keep putting it off. Hopefully this handy info-graphic will give you a good jumping off place to start with HIPAA. There is frankly a lot more to it than this, but if you start with these easy steps you’ll be farther along than you think. Check out this info-graphic and take your first steps today.
Why HIPAA Compliance?
HIPAA regulations recognize that personal health information (PHI) is sensitive data. It can social security numbers, as well as addresses, phone numbers, and many other information that would allow an individual to be easily found. Regulations have been put in place to safeguard this private medical data for the good of all involved.
The purpose of HIPAA is 4-fold. They want to make healthcare data portable so that patients can get excellent care no matter where they reside. This data should be able to easily follow them when they switch jobs or insurance providers. This allows them to give excellent care and make better decisions when they have an entire medical history.
They want to protect the integrity of that data. For this data to be usable it has to be protected. Basic security protocols should be followed to ensure that this data is protected against threats, backed up regularly, and in a state that is usable when needed.
They want to keep it confidential. Peoples medical histories are their own. This data should never be used except under HIPAA guidelines to provide excellent patient care. This data should be private and should never be used for marketing or any other purposes.
Lastly Accountability. These regulations were put in place to give some accountability to healthcare professionals in the way they handle patient data. They also put in place penalties associated with practices that do not comply with the standards and have a breach of patient data. These can be severe in the case of extreme negligence.
Three Categories of Safeguards
HIPAA is broken into three different categories of safeguards that have associated rules and regulations. They can be a little dense to decipher, but there are essentially administrative, physical, and technical safeguards.
Administrative
Administrative safeguards are exactly what they sound like. They instruct healthcare professionals that they must have a security management process in place. This process should implement procedures to prevent, detect, contain, and correct security violations.
These guidelines set policies on how to deal with employees that fail to comply with security policy. They should also include risk management analysis, as well as a full set of written policies that are given to every employee.
They strive to limit access to PHI to only what employees need to do their job, and they should also include a plan for how to quickly terminate access to PHI for employees that leave the organization.
Policies should also be in place for the ongoing training of employees on how to keep secure and maintain patient data integrity.
All of these policies and more should be established in order for a healthcare organization to be on their way to HIPAA compliance.
Physical
There are numerous physical safeguards that also need to be in place to achieve compliance. The main point of this is to limit the access to any of the systems that house PHI. This can be as simple as putting all servers that contain the information behind a locked door. If your server is sitting on a desk in plain view where someone could pick it up and walk off with it, that’s a problem.
Security systems can be a big help as well. They can not only control access to a given room or hallway, but scanning a badge also keeps a record of who had access when. In case of a breech this can be a big help in identifying the culprit.
Record keep on hardware is a part of physical security as well. Any computer containing PHI must have some record of where it goes if it gets moved. In addition, at the end of the life-cycle proper procedures must be in place to safely remove all PHI from that machine before it leaves the premises. All electronic media should also be disposed of in a proper manner at the correct age.
Technical
There are numerous technical safeguards that should also be in place. Start simple by ensuring that every employee has a unique login to access any system with PHI. Shared or common logins such as nurse1 or similar should not be used under any circumstances.
Business class firewalls should be put in place and set up by an IT professional. This gives you a layer of protection between your network and the outside world. A properly set up firewall can prevent a lot of common attacks.
Lockouts should be set on all machines on the network that access PHI. This means that the screen will automatically lock after a predetermined period of inactivity. This protects your organization should a nurse or doctor get busy and walk away from a computer leaving private information accessible. These can be centrally administered over the network via group policy.
Encryption should be used on all devices that have PHI to protect the data. Emailing patient data should be avoided, but if necessary this should also use an encrypted email solution that allows for secure transmission of medical records.
Audit controls should be put in place to give you a physical inventory of all of your hardware. This allows the organization to track all hardware containing PHI, and potentially issue a remote wipe command if any equipment were to go missing.
Patches and updates from Microsoft should be applied in a timely manner. Records should be kept of what patches have been applied to ensure security compliance.
Backups should be kept both locally and offsite. This allows you to quickly recover from a failure, but also helps you to ensure the integrity of that data should there be a major disaster such as fire, theft, or flood.
There is a lot to do
Reading through this brief summary of some of the requirements you may feel overwhelmed. It is a huge project, and one that will likely be ongoing for the history of your organization. Know that help is out there if you need it.
Help is here if you need it
i.t.NOW has been working with folks in the healthcare field for years, assisting them with their day to day support needs. We also know network security and can help your organization to protect PHI and get on your way to HIPAA compliance. We know what maintenance needs to be done, how to set up security, and what policies need to be in place. We can help to take a lot of the stress out of HIPAA compliance and streamline the process for you.
Call us today, and we can take the first steps towards HIPAA compliance together!