Our October 2024 i.t.INSIGHTS Newsletter is packed with essential cybersecurity tips, industry news, and a FREE Cybersecurity Checklist to help you protect your business from growing cyber threats. 📊🔐 💡 What’s inside? Strengthen your cybersecurity posture and stay ahead of the latest threats. Download the newsletter now and get your business cyber-ready! 🛡️ 👉 Download […]
Tag Archives: IT Security
So, you’ve been hearing a lot about cloud computing. If you’re anything like me, you’ve probably had a moment or two where you’ve wondered, “Is my data actually safe up there in the… well, cloud?” This is one of many cloud security myths that make businesses miss out on the capabilities that the right cloud […]
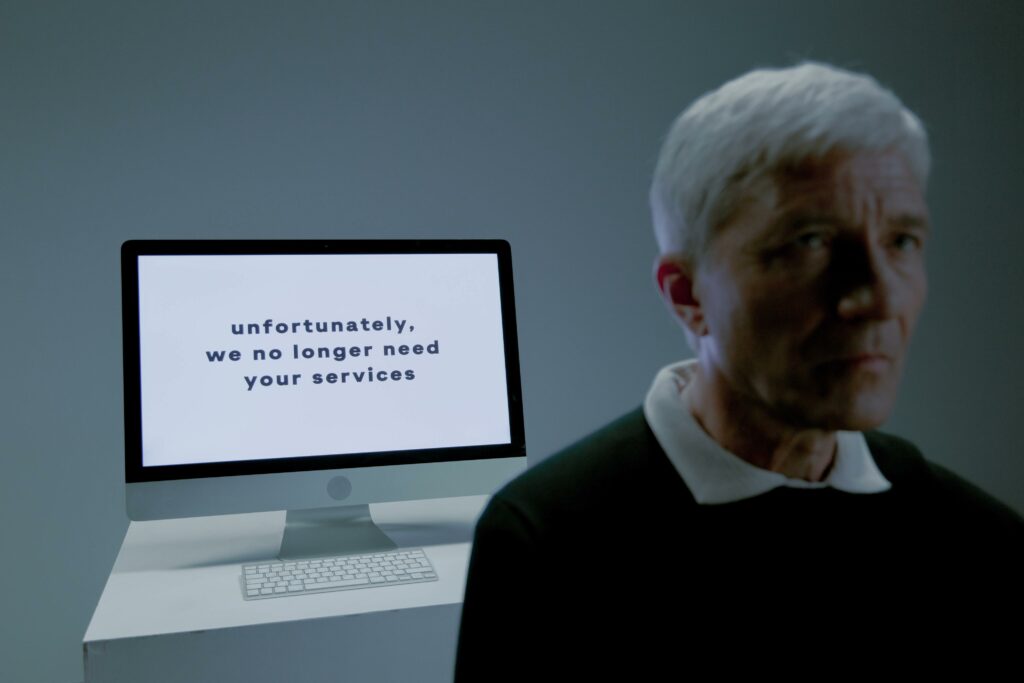
Time to address one of the most notorious IT blunders that organizations fall victim to: the employee offboarding. Seems simple, right? “We have a user leaving… abruptly. We need their access cut off… quickly.” The combination of not defining what this means and the time sensitive nature of some of these requests is a perfect […]
Most organizations make cybersecurity overly complicated because “you should do it either way.” This is not a valid argument. Business owners have tons of “have to” being thrown at them every day. It’s extremely difficult to cut through the fluff and identify what is critical and what is just nice to have. We take the […]
With the recent congressional hearing on TikTok security and data privacy rules, we thought we might take a slight deviation from our typical coverage to discuss a topic that is on a lot of lips. Along with some comical moments that highlighted almost complete ignorance from several members of congress on how the internet works, […]
There are a lot of business reasons why you may want to send encrypted email. It could be sensitive financial data, or personal information about employees. Maybe you work in healthcare and need to send personal health information that is protected by HIPAA. There could be several other reasons. There’s also not only one way […]
Digital inclination has brought about a new wave of cybercrime, with cyberattacks increasing at an unprecedented rate. Statistics from Abnormal revealed that phishing had a growth rate of 48% from previous years as of June 2022. Unfortunately, small and medium businesses (SMBs) are a common target for cybercriminals, accounting for 43% of cyberattacks in 2019 […]
We’ve been told for some time that there are dangers associated to connecting to free public Wi-Fi. What are those dangers? Could they put your data at risk? We’ll look at a few of the most common threats associated with public Wi-Fi, and how to stay protected. MITM Attack One of the biggest dangers with […]
i.t.NOW works hard to protect our clients’ networks from security threats and ensure their safety and operability. In those efforts we frequently see what growing threats there are in the wild. Two that we particularly wanted to make our clients aware of are Business Email Compromise (BEC) attacks, and Ransomware. Neither one of these attacks […]
Multifactor Authentication has become a part of our modern world. Its an essential part of a network security plan. However, hackers are using evolving attacks to defeat MFA. Let’s look at some of those attacks and see what can be done to protect against them. What is Multifactor Authentication? “Deploying MFA means you require more […]