The reporting that most IT service providers give you isn’t great. This week I sat with a potential client that was frustrated with their current IT provider because they asked for a hardware inventory. What they got back was a long list of computer names and IP addresses. It honestly looked like nonsense to the […]
There are a ton of cyber security frameworks out there. Depending on your line of business you may have become acquainted with NIST, HIPAA, PCI DDS, ISO/IEC, SOC, or others. There are a lot of commonalities amongst these frameworks with complexity being foremost. We want to break some of that complexity down. Starts with Questions […]
Business Owners and executives work hard to align spending with company objectives. They budget carefully to make the most out of every dollar. However, if you’re the owner or CFO of a small business and don’t have an IT background, how can you be confident in your IT budget allocation? Many owners ask themselves, “Am […]
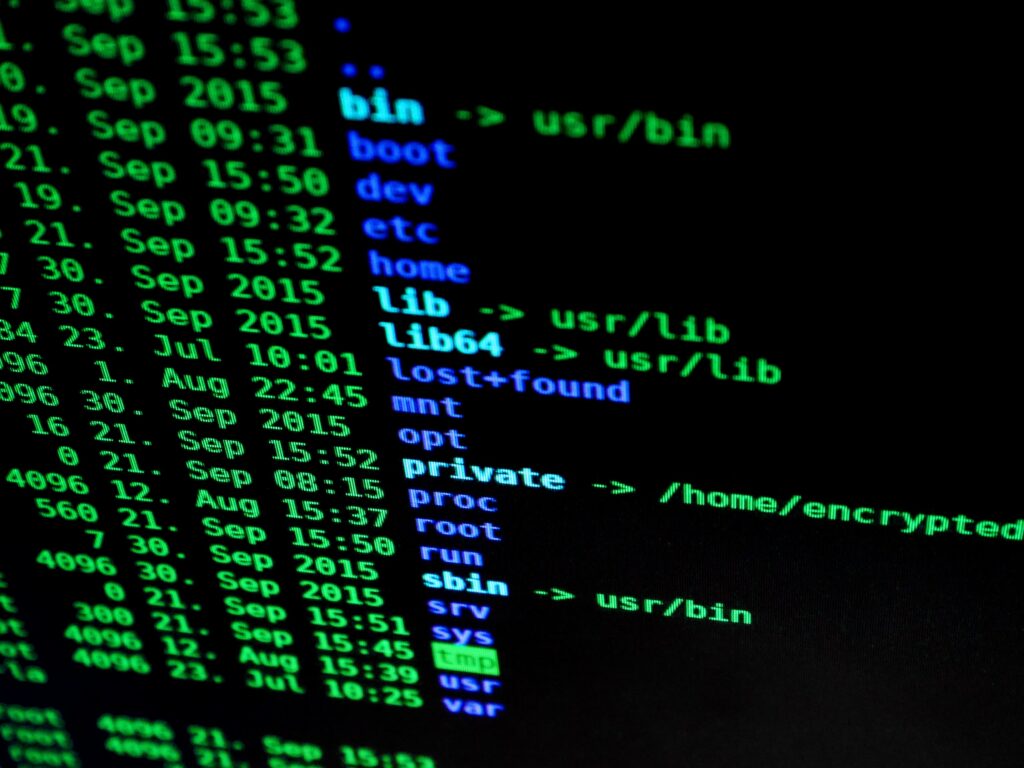
Users of the 3CX voip phone system should be on high alert. A new 3CX security vulnerability has been discovered which can deliver malicious payloads. This attack is worse than most because it is a supply chain attack. That means that the bad actors have managed to get their malicious code incorporated into the legitimate […]
With the recent congressional hearing on TikTok security and data privacy rules, we thought we might take a slight deviation from our typical coverage to discuss a topic that is on a lot of lips. Along with some comical moments that highlighted almost complete ignorance from several members of congress on how the internet works, […]
Recent conversations with potential clients about their current IT providers have once again highlighted some of the common red flags we see in our industry. If you’re struggling with any of these items, it might be an indication that there are serious organizational issues with your current IT provider that aren’t easily resolved. If you […]
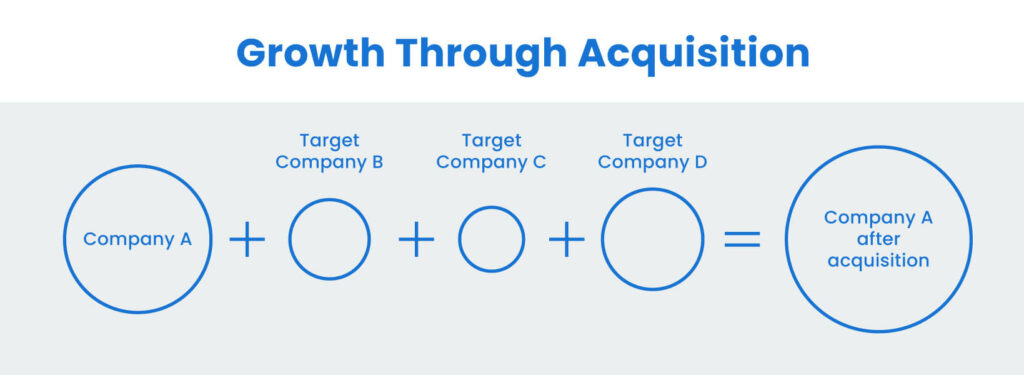
Recently we’ve been having a lot of conversations with companies that operate on the strategy of growth by acquisition. They span various industries. Property management, skilled nursing, assisted living, and most recently volleyball clubs. Regardless of the business vertical they are all buying new properties/facilities/clubs to fuel their growth. With that comes some potentially unique […]
There are a lot of business reasons why you may want to send encrypted email. It could be sensitive financial data, or personal information about employees. Maybe you work in healthcare and need to send personal health information that is protected by HIPAA. There could be several other reasons. There’s also not only one way […]
Digital inclination has brought about a new wave of cybercrime, with cyberattacks increasing at an unprecedented rate. Statistics from Abnormal revealed that phishing had a growth rate of 48% from previous years as of June 2022. Unfortunately, small and medium businesses (SMBs) are a common target for cybercriminals, accounting for 43% of cyberattacks in 2019 […]