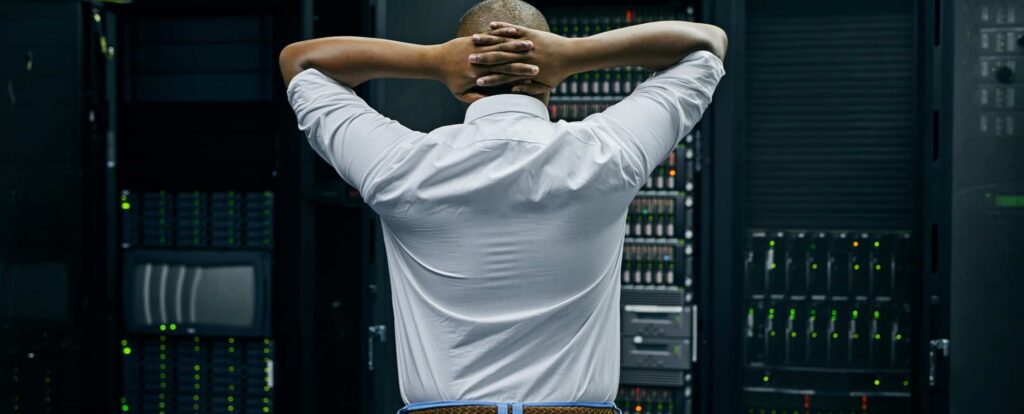
We met with some business owners this week where the current IT provider has neglected their technology for some time. There were a few contributing reasons for this. The client is in manufacturing and is hesitant to invest money in technology that they didn’t see improving their production process or output. The current solution was […]
There have been a lot of changes over the last few years to how we work. The rise of work from home has brought with it several new challenges like recovering your business hardware from terminated WFH employees. We have seen a few different businesses’ takes on that and have been involved on the IT […]
There is a lot of debate around backing up data stored in cloud solutions and SaaS applications. Office 365 backups are at the center of that debate. So, do you need to backup data stored in your SaaS apps? That depends. Do you need to backup data stored in Office 365? Almost certainly. Responsibility model […]
Since back in 2008 Verizon has been putting out a report each year called the Data Breach Investigation Report (DBIR). In 2013 they first wrote about ransomware. Social engineering was already happening and growing in popularity with bad actors. The latest edition of DBIR shows that 9 years later Ransomware and Social Engineering are still […]
I recently attended an IT industry conference where the topics were understandably cyber security heavy. One of the speakers that stuck out to me was Scott Augenbaum. Scott is a retired FBI agent that worked in the cybercrimes division for the last 20 years and has recently retired. A few things from his address stuck […]
As the saying goes, you’re only as strong as your weakest link, and in the case of cybersecurity, your weakest link is humans. With the new security challenges brought about by remote work, humans have become more of a cyber risk than ever. As of 2022, 88% of data breaches are caused by human error. […]
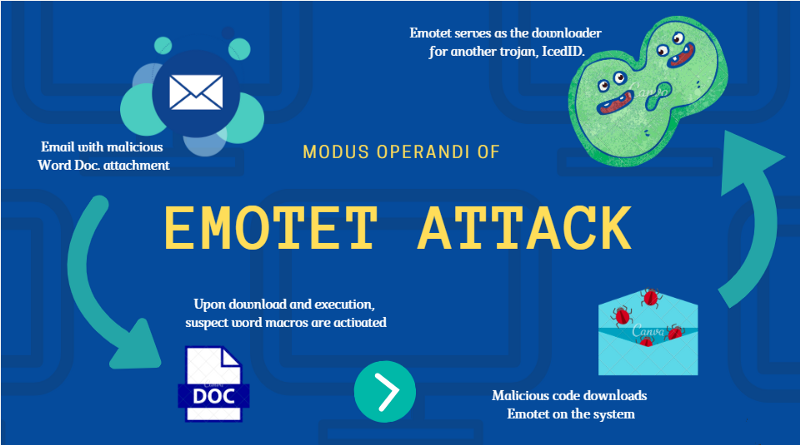
For several years bad actors have been using Emotet malware and its variants in large scale phishing attacks. These attacks are meant to compromise business email accounts and then allow them to deliver a payload of ransomware. Some recent updates from Microsoft have made those attacks less effective, so the hackers have had to pivot. […]
The weakest link in most IT security plans is frequently your employees. Cyber security training can help them recognize threats and not fall for that phishing scam. Without it, a misguided click can subvert a lot of the other security you’ve worked hard to put in place. What is Cyber Security Training? People make mistakes. […]
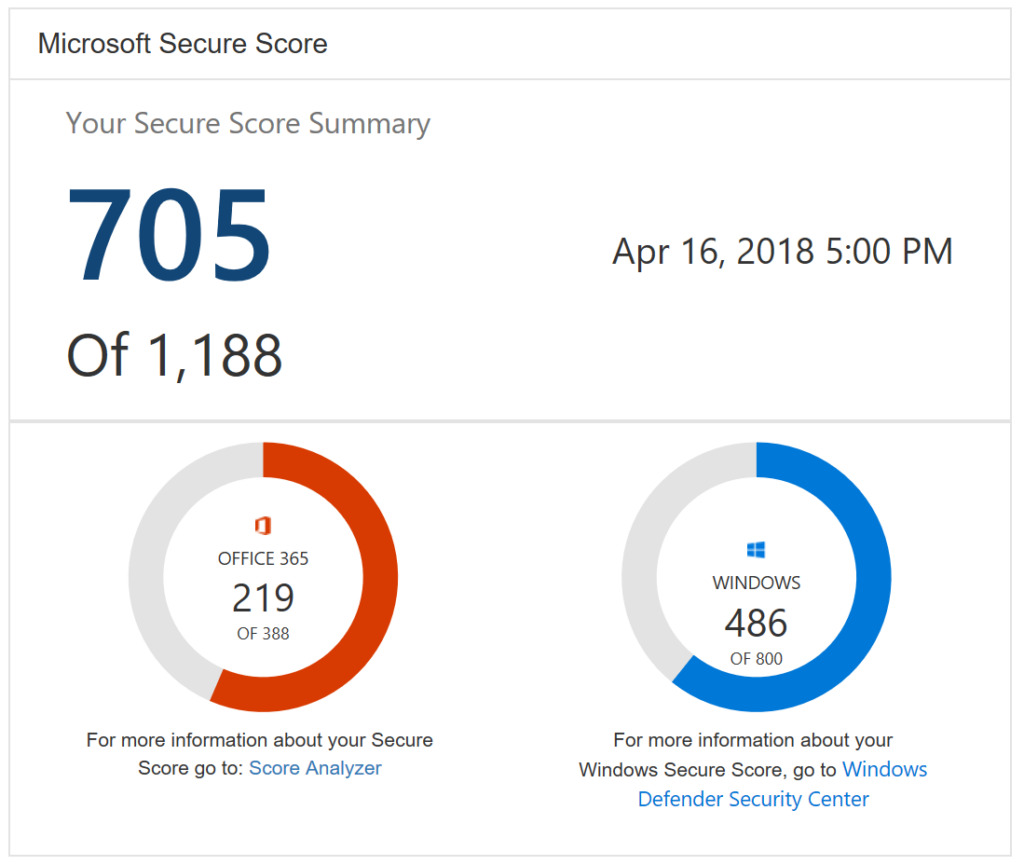
Businesses should always be on the lookout for ways that they can increase their security posture. Microsoft is aware of this and wants to help. They’ve created some built in functionality within Office 365 that assists organizations in improving their security. Here’s what it is and how it can help your business. What is Microsoft […]
With the rise of ransomware and increasing automated bot attacks the need for cyber liability insurance has never been higher than right now. Business owners often underestimate the cost of a breach or outage due to an attack. Having the right Cyber Liability insurance in place can help protect your business if you qualify. Security […]